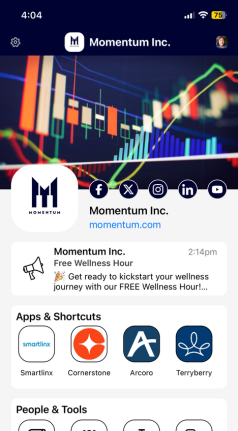
Operational success comes from meaningful engagement and data informed decisions-making.
Learn More




For more than a decade, companies have depended on Workrede to simplify access to their employees. We are proud to serve these innovative companies and deliver transformational business outcomes that positively impact their bottom lines.


Copyright © 2024 Workrede